April 13, 2026 Hyperbridge Exploit: 1 Billion Fake Bridged DOT Minted on Ethereum — The Wake‑Up Call for Every Wrapped Asset Holder

Have you ever looked at a “wrapped” token in your wallet and thought, “It’s basically the real thing, right?”
What if I told you that today—April 13, 2026—someone minted 1,000,000,000 fake bridged DOT on Ethereum, and turned that counterfeit into real money anyway?
The uncomfortable truth: the native chain can be perfectly healthy… and the wrapped version can still blow up in your hands.
In this post I’m going to explain (in plain English) why wrapped assets can fail even when the original blockchain is fine, why this Hyperbridge incident is so unsettling, and how you can judge risk the next time a “bridged” token looks just as trustworthy as the real thing.

The pain: wrapped assets can fail even when the native chain is healthy
Let’s get one thing straight: Polkadot didn’t “break” today. DOT didn’t magically get printed on the Polkadot network.
The weak point is the thing sitting between chains: the bridge and its wrapped/bridged representation on another network (in this case, Ethereum).
When you hold a wrapped asset, you’re not just trusting the original chain anymore. You’re trusting a whole extra stack of moving parts, like:
- Bridge smart contracts (the code that mints/burns the wrapped token)
- Relayers / validators (the actors who report or prove cross-chain events)
- Message verification (the logic that decides whether a “mint” is allowed)
- Admin keys / multisigs (who can upgrade contracts, pause the bridge, change settings)
- Upgrade paths (the exact mechanism projects use to patch—also a mechanism that can be abused)
So even if the underlying chain is secure, a bridged token can still become “real-looking counterfeit money” if the bridge layer gets tricked, misconfigured, or exploited.
This is not just theory. Bridges have been one of crypto’s biggest loss magnets for years. For example, Chainalysis reported that in 2022, bridge attacks accounted for over $2 billion in stolen funds across multiple incidents—because bridges concentrate trust and liquidity in one place.
What made this exploit so unsettling (even though “only” ~$237K was taken)
At first glance, some people will shrug and say: “Okay, but the attacker only extracted around $237K. That’s not a billion-dollar hack.”
That reaction misses why this incident hits a nerve.
Minting 1,000,000,000 fake bridged DOT is a giant red flare for any wrapped asset holder because it breaks the basic assumption that makes wrapped tokens usable in DeFi:
- Supply assumptions get shattered. If a wrapped token can be minted without backing, the “1:1” story becomes a marketing slogan, not a guarantee.
- Confidence cracks fast. Once traders suspect a wrapped asset might be unbacked, liquidity dries up, spreads widen, and panic selling can start.
- DeFi composability becomes a weapon. Counterfeit wrapped tokens can move through swaps, pools, and aggregators quickly—sometimes before dashboards and alerts catch up.
- The damage isn’t only what’s stolen. The bigger blast radius is trust: protocols that listed the token, LPs who provided liquidity, and holders who assumed “bridged = safe.”
And here’s the part that keeps happening in crypto history: when counterfeit-like supply appears, the market often punishes everyone holding that asset—long before a clean technical explanation shows up.
What I’ll help you walk away with
If you’re reading this with bridged assets in your wallet (DOT, ETH, BTC, stables—anything), my goal is simple: you should leave with a sharper instinct for when “wrapped” is convenient… and when it’s quietly dangerous.
In the rest of this post, I’ll give you:
- A clear timeline of what happened today and how it unfolded
- A simple breakdown of how this kind of minting typically becomes possible (no developer jargon required)
- A practical checklist you can use to judge bridge and wrapped-asset risk before you park serious value there
Because the real skill in crypto isn’t just picking good assets—it’s spotting the hidden trust layers that can break them.
Quick definitions (so the rest of the post is easy)
Let’s lock in a few terms, so the next sections read like a conversation, not a textbook.
Bridged token / wrapped asset
A token on Chain B that represents an asset from Chain A. Example: “bridged DOT” on Ethereum is supposed to represent DOT that exists natively on Polkadot.
Mint/burn model
A system where wrapped tokens are minted when the real asset is locked/verified, and burned when you redeem back to the native chain.
Lock-and-mint bridge
A common design where the real asset gets locked (or accounted for) on one side, and a wrapped version is minted on the other side. If the “lock” proof can be faked, the mint can be abused.
Canonical bridge vs third-party bridge
A canonical bridge is the “official” route a project ecosystem expects users to use (often maintained or endorsed by core teams). A third-party bridge is built by an external team. Both can fail—but they don’t carry the same trust assumptions.
Paused bridge
When a bridge is paused, transfers and/or redemptions may stop. That can protect the system from further damage, but it can also leave holders stuck holding a token that can’t be redeemed at the worst possible time.
Now for the question that matters: how did one exploit mint a billion fake bridged DOT on Ethereum—and still turn it into spendable value in the same move?
Next, I’ll walk you through exactly what happened on April 13, 2026, in a way you can follow even if you’ve never read a smart contract in your life.
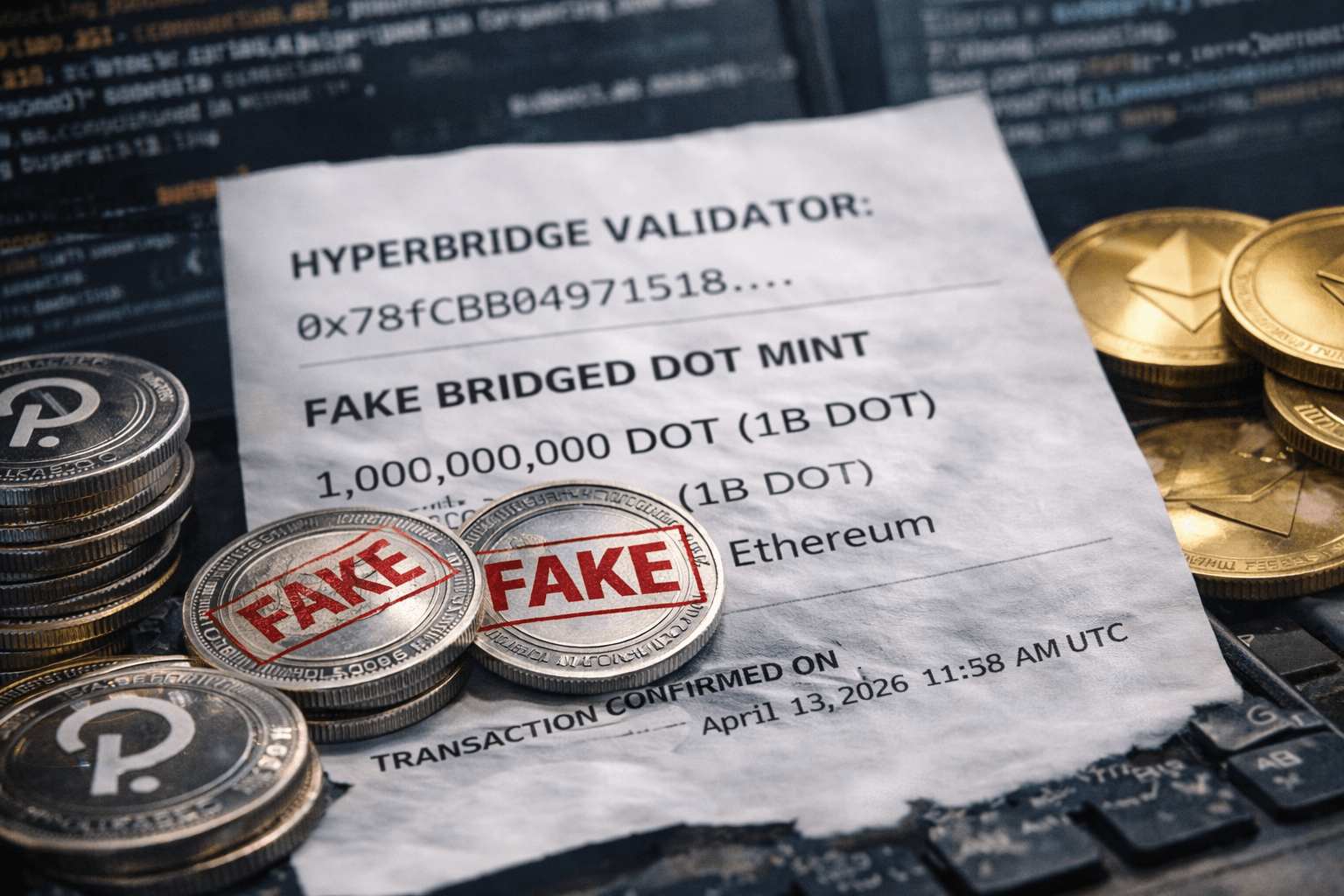
What happened on April 13, 2026: the Hyperbridge fake bridged DOT mint
Here’s the clean version of the mess:
On April 13, 2026, an attacker minted 1,000,000,000 “bridged DOT” on Ethereum via Hyperbridge, then managed to extract roughly $237K in value — and yes, it appears a big chunk of the extraction happened in a single transaction (the kind of atomic “do-everything-now” move that leaves almost no time for humans to react).
The important detail that keeps getting lost in the panic posts: Polkadot itself was not compromised. No native DOT was magically printed on Polkadot. This was a breakdown in the representation layer — the bridge token on Ethereum that is supposed to map to “real DOT somewhere else.”
As a containment step, the bridge was paused. That’s the right emergency lever to pull… but it also tells you something uncomfortable: redemption and normal movement can become a permissions problem the moment things go sideways.
If you want the live public breadcrumbs as they developed, I’m tracking the key threads here:
- Arkham alert thread
- Polkadot official statement
- Coin Bureau coverage
- The_CoDEFi thread
- thisisksa notes
- _Dragnipur_ analysis
A clear timeline readers can follow (minute-by-minute style)
Because public timestamps vary by source and reposts, I’m going to keep this as a sequence you can map onto the on-chain times you see in explorers and alert feeds:
- T+0: Abnormal mint occurs — 1B bridged DOT is created on Ethereum (the “should be impossible” moment).
- T+1 to T+2: Tokens begin moving immediately. No “testing” transfers, no slow rollout — this is the speed you see when a script is prepared in advance.
- T+2 to T+5: The attacker routes through available liquidity — typically this means swapping into assets that are easier to cash out (stablecoins, ETH, or highly liquid majors), or using a path that touches multiple pools to reduce reverts.
- T+5: Alerts start firing publicly (on-chain watchers are fast, but they’re not faster than a pre-built atomic transaction).
- T+5 to T+15: Teams and community accounts acknowledge the issue; partial details hit X; people scramble to figure out if Polkadot itself is affected.
- Shortly after: Bridge activity is paused to stop further minting / movement through the official mechanism.
About that “one transaction” detail: when you see a heist described that way, it usually means the attacker used an atomic bundle where actions happen back-to-back in a single Ethereum transaction:
mint → swap → swap → exit (and optionally: repay flash liquidity)
No waiting, no “send to another wallet and think,” and far fewer opportunities for defenders to interrupt the flow.

“Polkadot is fine” — what that actually means (and what it doesn’t)
When I say “Polkadot is fine,” I mean something very specific:
- Polkadot consensus wasn’t broken. No chain reorg, no validator set takeover, no native protocol-level failure implied by this mint.
- Native DOT supply on Polkadot wasn’t inflated by this event.
- Your DOT on Polkadot didn’t suddenly become counterfeit because a bridged version on Ethereum was abused.
But here’s what “Polkadot is fine” doesn’t mean:
- The bridged DOT token on Ethereum is fine. It isn’t. Once unbacked minting is possible (even briefly), the market has to assume the wrapper can be manipulated again until proven otherwise.
- Redemption is guaranteed. If the bridge is paused, redemption can become delayed, throttled, or subject to governance/emergency procedures.
- DeFi positions are safe. If a wrapped asset depegs or gets blacklisted/paused, lending markets and LP positions can get wrecked even if the underlying L1 is perfectly healthy.
That split — “native chain healthy, wrapper unhealthy” — is exactly why wrapped assets can feel stable… right up until the moment they aren’t.
How can fake bridged tokens even exist?
Most bridges are basically a promise engine with receipts:
- Some amount of “real” asset is locked (or otherwise accounted for) on Chain A.
- A message is produced that says: “Lock happened, here’s proof.”
- A contract on Chain B verifies that message and then mints the wrapped/bridged token.
So where does it break?
It breaks when the thing responsible for saying “yes, that lock really happened” can be tricked, bypassed, forged, or overridden. The ugly versions usually look like one of these:
- Message verification bug: the contract accepts a message it shouldn’t.
- Authorization failure: a relayer/validator set (or signing threshold) is compromised, misconfigured, or spoofed.
- Accounting mismatch: the bridge believes funds are locked when they aren’t (or counts the same lock twice).
- Upgrade/admin key risk: an admin path can change logic or permissions in a way that enables unauthorized minting.
And once the mint function is reachable without real backing?
“Wrapped” stops meaning “backed.” It turns into “printed.”
This isn’t theoretical fear-mongering either. Studies and industry reports have been yelling about this class of risk for years. For example, Chainalysis’ 2022 research on cross-chain bridge attacks highlighted that bridge compromises were responsible for a huge share of stolen funds in that cycle (north of $2B in some tallies). Different year, different bridge, same core lesson: the verification layer is the battlefield.
Why the attacker “only” took ~$237K when they minted 1B DOT
This is the part that tricks people:
They see “1B minted” and assume “1B stolen.” That’s not how it works in practice.
The attacker can mint an absurd number, but they can only extract what the market will actually give them before everything collapses. The real limiter is usually:
- Liquidity depth: pools only have so much real value sitting in them.
- Price impact: dumping a huge amount nukes the price, so each next token sold gets you less.
- Arbitrage + bots: as soon as the price diverges, bots race in (sometimes to profit, sometimes to reduce exposure), and conditions change fast.
- Pauses / guards: once teams detect the exploit, they shut doors (or LPs yank liquidity).
Think of it like counterfeiting casino chips. Printing a truckload is easy if you can access the printer. Cashing them out is where you hit the real-world constraint: how much money is in the cage, how quickly security reacts, and how fast you can move without getting blocked.
So “minted amount” is mainly a severity signal. “Realized profit” is the liquidity reality.
What this means for every wrapped asset (not just DOT)
If you hold any asset that depends on cross-chain verification, you should read today as a general warning — not a DOT-only story.
This includes things people often treat as “basically the same as the real thing,” like:
- Bitcoin wrappers (WBTC-style designs, or any BTC representation on another chain)
- Bridged ETH and bridged stablecoins
- Liquid staking / restaking wrappers when they hop chains or stack multiple layers of representation
- Any token issued by a bridge that relies on a signer set, guardians, or a proof system you can’t easily verify yourself
The uncomfortable pattern is that wrappers tend to behave like the real asset… until a single point in their trust chain breaks.
The uncomfortable truth: bridges are “blockchain risk multipliers”
I treat bridges like leverage — not financial leverage, but risk leverage.
You’re not just taking “smart contract risk.” You’re stacking:
- Smart contract risk (bugs, edge cases, integration failures)
- Relayer/validator risk (key compromise, collusion, downtime, misconfiguration)
- Governance/admin key risk (upgrades, emergency controls, who can pause/modify what)
- Liquidity risk (can you exit without eating massive slippage?)
- Monitoring latency (the time between “exploit starts” and “pause happens”)
And yes — audits help, but they’re not a forcefield. An audit is a snapshot of code and assumptions at a moment in time. Bridges fail in the gaps: deployment configs, signer operations, upgrades, message parsing edge cases, and incentives.
Reader FAQ: “Which blockchain technology was first outlined in 1991 by Stuart Haber and W. Scott Stornetta?”
It was an early form of blockchain — a chain-of-blocks timestamping system designed to make tampering with records obvious.
That foundational idea is strong, and it’s a big reason why mature L1s can be resilient.
But today’s incident is the reminder that bridges aren’t protected by that original security model by default. A bridge is a separate system glued on top — and it can fail even if the underlying chain is doing everything right.
Where I’m tracking updates and public statements (quick links, not the whole story)
If you want to follow the public trail without getting lost in quote-tweet chaos, these are the threads I keep coming back to:
Now the question I want you to answer for your portfolio is simple:
If one of your wrapped assets got paused tonight, would you know exactly what to do in the next 10 minutes?
Because that’s the difference between “annoying headline” and “I just got stuck holding the broken version.” In the next section, I’m going to give you the exact checklist I use to judge whether a wrapped token is safe enough to touch — and what I do when it isn’t.
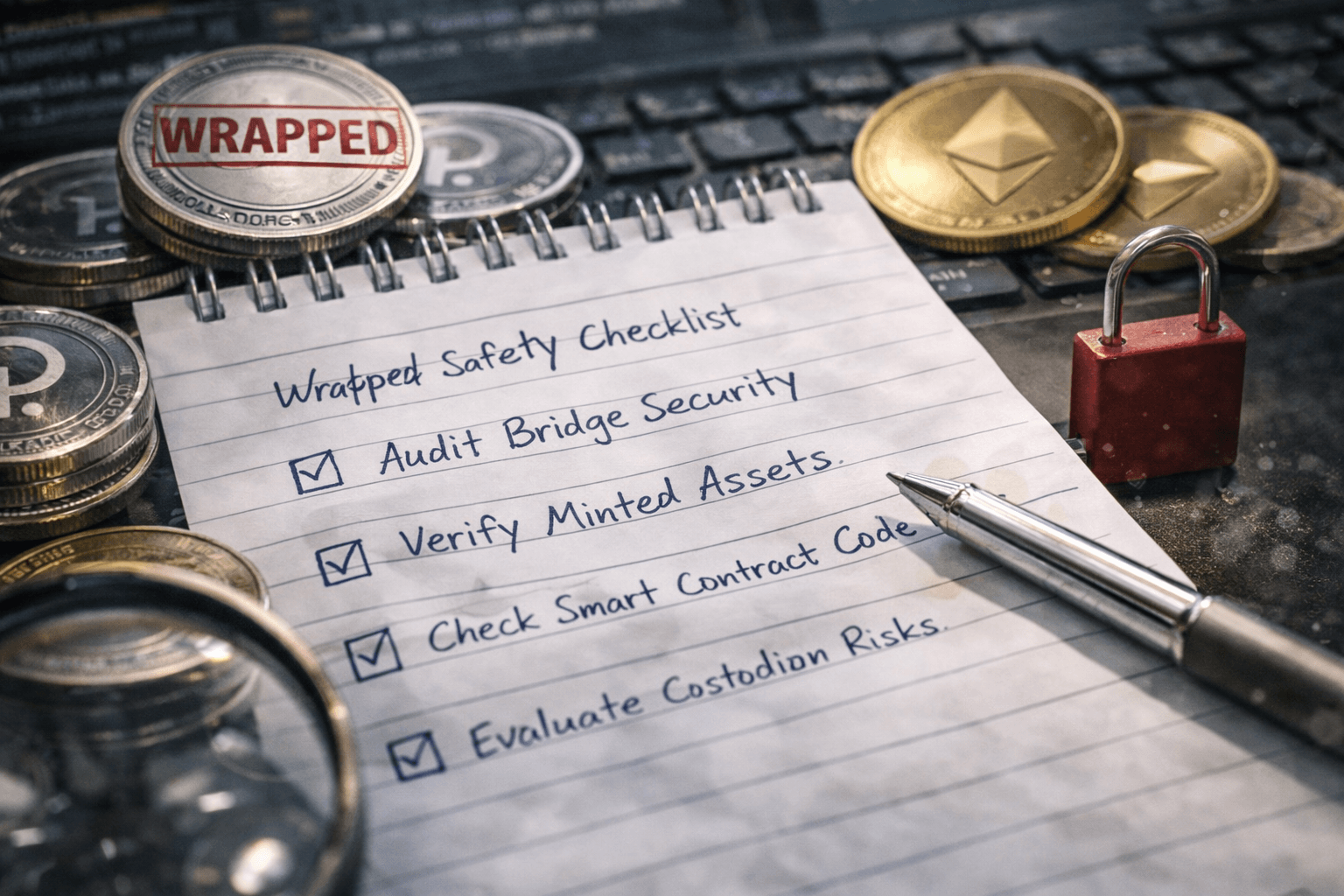
What I want you to do next: a practical safety checklist for wrapped assets
If today’s Hyperbridge mess taught me anything (again), it’s this: a wrapped token is not “the same asset on another chain.” It’s an IOU with a security model glued on top.
So here’s the checklist I personally use before I treat any bridged/wrapped asset like “real money.” Bookmark it. Use it. Send it to the friend who thinks every token with a familiar ticker is automatically safe.
Rule of thumb: if you can’t clearly explain how the token is minted, redeemed, and governed, you’re not holding “the asset.” You’re holding trust.
- 1) Confirm you’re using the canonical bridge (not “a bridge”).
“Bridged DOT” can exist as multiple ERC-20s from different teams. Only one might be the official or most battle-tested route.What I do: I start from the official ecosystem docs and follow the link to the bridge UI, then click through to the contract address and match it on Etherscan. If a random DEX list shows a token first, I assume it’s a trap until proven otherwise. - 2) Read the mint/burn + backing model in plain English.
You want a simple answer to: “What must be true on Chain A for tokens to be minted on Chain B?”Green flags:- Clear lock/mint or burn/redeem flow explained publicly
- Backed supply can be verified on-chain (or via a widely used dashboard)
- Redemption is not “best effort” or dependent on a human approval step
- 3) Check whether redemption is permissionless.
This one is huge. If you can’t redeem without an admin, a multisig, or a “support ticket,” then your token can trade at $1 today and $0.10 tomorrow the moment confidence cracks.What I look for: a public function path that lets me burn wrapped tokens and claim the native asset without special permissions. If the docs are vague (“redemptions processed periodically”), I size my position like it’s high-risk. - 4) Identify upgrade/admin keys (and whether there’s a timelock).
Upgradeable contracts are not automatically bad. Hidden, instant upgrades are.What I do (quick version):- Check Etherscan for “Proxy” patterns and the Implementation address
- Look for roles like owner, admin, pauser, minter
- Find out if changes go through a timelock (hours/days) or can happen instantly
A timelock won’t stop every exploit, but it can stop the worst kind of silent overnight changes.
- 5) Understand the proof model: light-client vs multisig/validators.
Bridges generally land somewhere on a spectrum:- Stronger: on-chain verification using light-client / cryptographic proof systems (harder to fake, harder to operate)
- Weaker: multisig / validator attestation (often practical, but adds human and key risk)
If it’s multisig/validator-based, I want to know: Who are they? How many signatures are needed? What’s the history of key rotation? Is there slashing? Is there public monitoring?
- 6) Watch the supply like you’d watch a heart monitor.
The scariest part of fake mint events is how quickly they distort the market before most holders even notice.What I use in real life:- Etherscan to watch total supply changes and mint events
- Dune dashboards for supply vs backing (if available)
- DeFiLlama to see liquidity depth and where the token is concentrated
- Arkham for entity tracking when things look off
Practical trigger: if supply jumps unexpectedly or backing can’t be reconciled fast, I treat the wrapped token as contaminated until proven clean.
- 7) Stress-test liquidity before you “trust” the price.
A wrapped token’s chart can look fine right up until it doesn’t. I check:- How much can I sell with <1% slippage?
- Is liquidity concentrated in one pool or spread across venues?
- Who holds LP tokens? Is it mostly one address?
If liquidity is thin, a single exploit transaction can turn the token into a falling knife.
- 8) Cap your exposure based on “bridge trust,” not token brand.
I don’t care how reputable the ticker is. I care about the wrapper.A simple sizing framework that’s kept me out of trouble:- Low trust bridge: I treat it like a speculative alt position (small, disposable)
- Medium trust bridge: I size it like a DeFi position that can get paused
- High trust bridge: still not “risk-free,” just “risk-managed”
- 9) Don’t ignore the data: bridges have been a top hack category for years.
If you want one reason to take this checklist seriously: history.Multiple industry reports have repeatedly flagged bridges as outsized targets because they concentrate value and add complex verification layers. For example, Chainalysis’ past security research highlighted how cross-chain bridge exploits accounted for a large share of stolen funds in several major years, and Immunefi’s incident reports consistently show cross-chain/bridge-style failures among the most damaging events by losses.You don’t need perfect numbers to act on the pattern: attackers love bridges because bridges are where the money piles up. - 10) Basic wallet hygiene still matters (especially in a panic).
When chaos hits, scams multiply.- Revoke old approvals you don’t need (I use tools like Revoke sites depending on chain)
- Don’t sign “migration” transactions from random links
- Keep a clean wallet for long-term holds and a separate one for DeFi
If you currently hold bridged/wrapped tokens: my damage-control playbook
If you’re reading this while staring at a wrapped token position and thinking, “Should I rush out right now?”—here’s the calm approach I follow.
- 1) Don’t market-sell into thin liquidity just to feel safe.
Panic selling is how you turn a scary situation into a guaranteed bad fill. First, check pool depth and slippage for your size. - 2) Verify whether minting/redemption is paused.
A pause changes everything. If redemption is paused, the token can trade like a distressed IOU. In that scenario, price can disconnect from “what it should be worth.” - 3) Compare three prices, not one.
- DEX price (what you’ll actually get if you sell now)
- CEX price (if it’s listed anywhere reputable)
- Redeem value (if redemption works, what you can redeem for)
When these diverge, the market is telling you confidence is broken—or liquidity is broken—or both.
- 4) Follow official comms, but verify on-chain.
I watch official announcements for operational updates (pause, patch, post-mortem timeline), but I trust on-chain behavior for the truth: supply changes, mint events, and contract upgrades leave footprints. - 5) Plan your exit like a firefighter, not a gambler.
If redemption reopens, I prefer reducing risk in steps instead of trying to nail the perfect moment. For bigger positions, I’ll split transactions to reduce MEV and slippage risk. - 6) Assume scammers will impersonate “support.”
The minute an incident trends, fake “bridge recovery” sites show up. I never connect my wallet from a link in replies, DMs, or paid ads.

What projects should learn (and what I’ll be watching after today)
I’m not interested in vague promises like “security is our top priority.” I’m interested in engineering and incentives that make this kind of failure harder to repeat.
- Real-time anomaly alerts on minting and supply.
If supply spikes, it should page humans immediately and trigger automated safeguards. The “we noticed on Twitter” era needs to end. - Hard limits and rate limits on mint paths.
If a bridge can mint “infinite” wrapped tokens in one go, you’ve built an attacker’s dream. Circuit breakers should exist at the contract level. - Stronger, simpler verification paths.
Every extra component—relayers, signatures, message parsing, upgrade hooks—is another place to mess up. Fewer moving parts beats clever complexity. - Transparent governance and key management.
Publicly documented signers, thresholds, rotation policies, and timelocks. If the community can’t audit who can mint/pause/upgrade, the bridge is running on vibes. - Post-mortems that actually answer the hard questions.
I want root cause, the exact check that failed, how it was exploited, what’s changing in code, and how you’ll prove it’s fixed (tests, audits, formal verification where appropriate).
And yes—I’ll be watching whether teams add public dashboards for backing vs supply and whether they make it easy for independent analysts to monitor risk without reverse-engineering everything.
Final thought: convenience has a cost
Wrapped assets are useful. They’re how liquidity moves, how strategies work, how ecosystems connect. But they are not magic.
A native chain can be perfectly healthy while the wrapper around its asset breaks. When that happens, your risk isn’t “crypto risk” in general—it’s the specific bridge’s design, keys, incentives, and response time.
If you take one habit from today, let it be this: before you park serious money in a wrapped token, treat it like you’re lending that money to a system. Because you are.
I’ll keep updating my reviews and filters so you can quickly sanity-check bridges and wrapped assets before trusting the next “it’s basically the same token” story.
